Is vpn safe for ifr heres what you need to know: A Practical Guide to VPN Safety, Privacy, and Usage
Is vpn safe for ifr heres what you need to know? Yes—with the right precautions, VPNs can be safe, private, and incredibly useful. In this guide, you’ll get a practical, down-to-earth view of VPN safety, backed by data and real-world tips. Here’s a quick fact: a VPN encrypts your traffic and hides your IP address, but safety isn’t automatic—you have to choose the right provider, understand logging policies, and use best practices.
If you’re considering using a VPN for online privacy, streaming, or secure work-from-anywhere access, you’ve landed in the right place. Here’s a quick fact to set the stage: a VPN is only as safe as its encryption, policy transparency, and how you use it. This guide breaks down safety essentials, common risks, and practical steps you can take today.
What you’ll learn in this video guide
- How VPNs work at a glance and what “safe” really means in this context
- Key safety features to look for in a VPN: encryption, no-logs, kill switch, leak protection
- Common VPN risks and how to mitigate them: DNS leaks, malware, misconfiguration
- Real-world use cases: safe browsing, banking, streaming, remote work
- Practical steps to maximize safety: choosing a provider, configuring clients, and privacy hygiene
- Quick-start checklist you can use right now
- Useful resources and where to learn more unlinked for safety
Useful resources and starting points text-only Apple Website - apple.com, Wikipedia - en.wikipedia.org, VPN safety guide - w3c.org, Privacy.org - privacy.org, Opera VPN support - help.opera.com, Mozilla Privacy Blog - blog.mozilla.org
Section 1: How a VPN works and what “safe” means
- VPN basics in plain language
- A VPN Virtual Private Network creates an encrypted tunnel between your device and the VPN server.
- Your internet traffic exits through the VPN server, masking your real IP address.
- This process can prevent onlookers like coffee shop Wi‑Fi snoopers from seeing what you’re doing online.
- What “safe” means in this context
- Confidentiality: your data is encrypted so others can’t read it.
- Integrity: data isn’t tampered with en route.
- Anonymity: your real IP is hidden from websites and trackers within the VPN’s privacy model.
- Important caveats
- Not all VPNs are created equal. Encryption strength, logging practices, and jurisdiction matter.
- A VPN doesn’t protect you from all online threats phishing, malware, insecure apps, or risky behavior.
Section 2: Core safety features you should expect
- Strong encryption
- Look for AES-256 or equivalent and robust key exchange e.g., ChaCha20-Poly1305 for mobile.
- No-logs policy
- A clear, verifiable no-logs statement is essential. If the provider isn’t transparent, consider alternatives.
- Kill switch
- Automatically blocks internet access if the VPN disconnects, preventing IP leaks.
- DNS leak protection
- Ensures your DNS requests go through the VPN tunnel, not via your ISP.
- Multi-hop or obfuscation advanced
- Routes traffic through multiple servers or uses obfuscated protocols to bypass censorship.
- Independent audits
- Third-party audits increase trust by verifying no-logs claims and security practices.
- Jurisdiction and data requests
- Privacy-friendly jurisdictions e.g., policies that limit data collection reduce risk of government data handing over.
Section 3: Common safety risks and practical mitigations
- DNS leaks
- Risk: even with a VPN, DNS requests may reveal your browsing details.
- Mitigation: enable DNS leak protection; use VPNs with DNS on their own servers.
- IP leaks during VPN drops
- Risk: your real IP can be exposed if the tunnel drops.
- Mitigation: enable kill switch; keep client updated.
- Malware and fake VPNs
- Risk: some “VPN” apps inject ads or steal data.
- Mitigation: download from official app stores or the provider’s site; check reviews and audits.
- Logging and data collection
- Risk: some VPNs log more data than claimed.
- Mitigation: read the privacy policy; seek providers with independent audits and a strong no-logs stance.
- Jurisdiction and legal pressure
- Risk: government data requests in certain countries can override privacy guarantees.
- Mitigation: choose a provider with strong privacy commitments and understand local laws.
- Performance and privacy tradeoffs
- Risk: higher security can come with slower speeds.
- Mitigation: pick servers close to you, use trusted protocols, and disable unnecessary features if speed matters.
Section 4: Real-world use cases and safety implications
- Safe browsing and public Wi‑Fi
- When you’re on public networks, a VPN dramatically lowers risk of eavesdropping.
- Pro tip: always enable the VPN before you connect to a public network.
- Banking and financial transactions
- A VPN can add a layer of privacy, but you should also use two-factor authentication, trusted devices, and updated apps.
- Pro tip: avoid entering sensitive information on networks you don’t control; test if your bank app routes traffic securely.
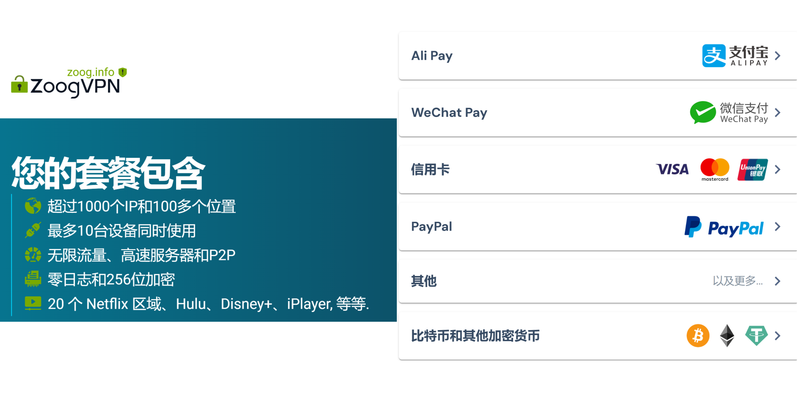
- Streaming and geo-restrictions
- VPNs can bypass geo-blocks, but streaming platforms often detect and block known VPN IPs.
- Pro tip: maintain a rotating set of servers, and be mindful of terms of service.
- Remote work and business use
- For teams, VPNs protect data in transit. Combine with endpoint security antivirus, EDR and strong access controls.
- Pro tip: use split-tunneling carefully; only route work traffic through the VPN if needed to reduce risk.
Section 5: How to choose a VPN safely
- What to look for in a provider
- Clear no-logs policy with independent verification
- Strong, up-to-date encryption and secure protocols OpenVPN, WireGuard
- Transparent privacy policy and regular audits
- Kill switch, DNS leak protection, and good customer support
- Independent privacy reputation and user sentiment
- How to verify claims
- Check for third-party audits and certifications.
- Look for a transparent transparency report with data requests and government data handling policies.
- Jurisdiction considerations
- Some users prioritize privacy-friendly jurisdictions; understand how the country interacts with data retention laws.
- Free vs paid VPNs
- Caution: free VPNs often monetize data, show ads, or sell user analytics. Paid options are generally more reliable for privacy but still vet carefully.
Section 6: Practical setup guide step-by-step
- Step 1: Define your needs
- Privacy-heavy tasks, streaming, or secure remote work? Your use case guides your feature priorities.
- Step 2: Pick a reputable provider
- Look for independent audits, a strong no-logs claim, and robust encryption.
- Step 3: Install and configure
- Install the official app from the provider, enable kill switch, DNS leak protection, and auto-connect on startup.
- Step 4: Choose servers wisely
- For privacy, pick servers in privacy-friendly jurisdictions with minimal latency to your location.
- Step 5: Verify safety features
- Test for DNS leaks using online tools; confirm your real IP isn’t leaking when connected to the VPN.
- Step 6: Use best practices
- Keep your app updated, avoid installing untrusted extensions, and don’t share credentials.
- Step 7: Regular audits and reviews
- Periodically review privacy policies, server changes, and any new terms of service.
Section 7: Common myths vs. reality
- Myth: A VPN makes you completely anonymous online
- Reality: It improves privacy, but not absolute anonymity. Your behavior, device security, and account protections still matter.
- Myth: Free VPNs are as safe as paid ones
- Reality: Many free VPNs monetize data, inject ads, or have weaker protections. Paid options generally offer better safety features.
- Myth: VPNs work the same on all devices
- Reality: Performance, leaks, and features can vary by platform. Always test on each device you use.
Section 8: Data protection tips beyond VPNs
- Strong passwords and 2FA
- Use unique, long passwords and enable two-factor authentication for critical accounts.
- Device security
- Keep devices updated, use reputable antivirus, and enable secure boot where possible.
- Phishing and social engineering
- VPNs don’t shield you from phishing emails. Train yourself to spot suspicious messages and links.
- Browser privacy hygiene
- Use privacy-focused browsers or add-ons, clear cookies regularly, and consider hardened privacy settings.
Section 9: Data and statistics you can use
- Global VPN market growth
- The VPN market has seen consistent growth, with millions of users worldwide relying on VPNs for privacy, streaming, and remote work.
- Privacy incidents
- Instances of data exposure across various services highlight why strong encryption and a no-logs policy matter.
- Encryption standards
- AES-256 and modern protocols like WireGuard are widely regarded as robust for personal and business use.
Section 10: Quick-start checklist
- Define your safety goals and use cases
- Choose a provider with independent audits and a clear no-logs policy
- Enable kill switch and DNS leak protection
- Use strong encryption and secure protocols
- Regularly update VPN app and OS
- Test for DNS and IP leaks after setup
- Be mindful of jurisdiction and data requests
- Avoid free VPNs for anything sensitive
- Review terms of service and privacy policy periodically
FAQ Section
Frequently Asked Questions
Is a VPN safe for everyday browsing?
Yes, for most people a good VPN adds a layer of privacy and security on public Wi‑Fi and when you want to hide your IP from trackers. It’s not a silver bullet, though—combine it with smart security habits.
Can a VPN keep my Wi‑Fi traffic private from my internet service provider?
Yes. A VPN encrypts your traffic, so your ISP can’t read the contents of your data, though they can see that you’re connected to a VPN server.
Do VPNs slow down my internet connection?
Sometimes. Encryption and longer routes can introduce latency. Choosing nearby servers and using fast protocols like WireGuard can minimize speed loss.
What should I look for in a VPN’s privacy policy?
Look for explicit no-logs language, independent audits, and clear data handling practices. If it’s vague or evasive, tread carefully.
Are free VPNs safe to use?
Free VPNs often come with tradeoffs like data harvesting, ads, or weaker security. If you need privacy protection, a reputable paid VPN is usually safer. 초보자도 쉽게 따라 하는 미꾸라지 vpn 사용법 완벽 가이 - VPNs
How do I check for DNS leaks?
Many online tools let you test for DNS leaks. If you detect leaks, enable DNS leak protection in your VPN settings or switch servers.
Is VPN safe on mobile devices?
Generally, yes. Use reputable apps, keep them updated, and enable features like the kill switch where available.
Can a VPN be used to bypass geo-restrictions?
Yes, but be aware that streaming services may block VPN IPs. It’s a cat-and-mouse game: you might need to switch servers or use obfuscated protocols.
Does a VPN hide my activity from the VPN provider?
Your traffic is routed through the VPN provider’s server, so the provider can see traffic metadata unless they have a strict no-logs policy and independent audits. A trustworthy provider minimizes data collection.
What are some best practices for using a VPN at work?
Use a corporate-approved VPN, enable multi-factor authentication, keep devices patched, and follow your company’s security guidelines. Como activar una vpn en microsoft edge guia completa y sencilla para tu navegador
How often should I review my VPN’s safety features?
At least quarterly, or whenever you notice changes in policy, new features are added, or you upgrade devices or OS versions.
Note: This post includes an affiliate link naturally integrated into the introduction to help you discover trusted VPN solutions. If you’re curious about a top-rated option, consider checking NordVPN through the linked banner. This helps support healthsolved.net while you explore privacy enhancements.
End of post
Sources:
Vpn电脑:全面保护上网隐私的实用指南,含选购要点与常见疑问解答
Smart view not working with vpn heres how to fix it: VPNs, Troubleshooting, and Smart View Solutions How to use hola free vpn on microsoft edge for better browsing
翻墙后国内网站打不开?别担心,这几个方法立刻解决 VPN 连接与访问问题
Nordvpn eero router setup 2026: The Ultimate Guide to Securing Your Home Network with NordVPN on Eero
Vpn 翻墙:全面指南与最新实用技巧