Troubleshooting Windows 11 FortiClient VPN IPSec Connection Failures: Quick Fixes, Pro Tips, and Expert Steps
Troubleshooting Windows 11 FortiClient VPN IPSec connection failures: you’re not alone—these issues pop up more often than people expect, and they’re usually fixable with a few targeted checks. Quick fact: most IPSec VPN problems on Windows 11 boil down to misconfigured security settings, blocked ports, or outdated client software. This guide walks you through practical steps in a friendly, easy-to-follow style, with real-world tips you can apply right away. What you’ll get:
- A step-by-step checklist you can follow in under 15 minutes
- Clear explanations for why each fix works
- Quick commands and settings you can copy-paste or apply with a click
- A summary of current stats and best practices to keep your VPN solid
Quick references and resources (not clickable here): Apple Website - apple.com, Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence, Fortinet Support - support.fortinet.com, Windows 11 VPN settings - support.microsoft.com, FortiClient VPN IPSec - FortiGate VPN IPSec, VPN security best practices - cisco.com, NordVPN - nordvpn.com
Understanding the problem: IPSec VPN basics and Windows 11 quirks
- IPSec (Internet Protocol Security) is a suite of protocols for secure network communication. When FortiClient uses IPSec, it relies on proper phase-1 (IKE) and phase-2 (IPSec) negotiations.
- Windows 11 brings stronger default security, which can block certain VPN configurations if the FortiClient client or the firewall isn’t aligned.
- Common symptoms:
- Connection fails at or before authentication
- Tunnel establishes briefly then drops
- Error codes like 0xc0020017, 0x8009030c, or 0x80072757 appear
- IPSec negotiation stalls on Phase 1 (IKE)
Pro tip: keep your FortiClient and Windows updates current. A lot of failures come from compatibility gaps that get fixed in patches.
Quick-win fixes: non-technical steps to try first
- Update everything
- Ensure FortiClient is the latest version supported by your VPN service
- Install Windows 11 updates including any security rollups
- Update network drivers (especially NIC and Wi‑Fi adapters)
- Reboot and re-test
- Sometimes a simple reboot clears stuck tunnel states or conflicting services.
- Check your network environment
- Try a different network (mobile hotspot or wired Ethernet) to rule out router issues
- Disable VPN blockers in corporate networks or antivirus VPN shields temporarily to test
- Verify credentials and server address
- Double-check the FortiClient profile: server IP/hostname, group name, username, and password or certificate
- If you’re using certificate-based auth, confirm the certificate chain is intact and not expired
- Examine the FortiClient logs
- Look for specific errors during IKE negotiation (Phase 1). Logs often indicate which door is closed (UDP ports, NAT traversal, certificates, etc.)
- Check firewall rules on Windows 11
- Make sure FortiClient is allowed through Windows Defender Firewall
- Open required ports (see detailed section below)
- Time and date accuracy
- IPSec is sensitive to clock drift. Sync time with an NTP server to avoid certificate validation problems
Networking and ports: what needs to be open
FortiClient IPSec typically uses:
- UDP 500 (IKE)
- UDP 4500 (NAT-T)
- UDP 1701 (if L2TP is used; often not required for FortiClient IPSec)
- ESP protocol (IP protocol 50)
If your router or firewall blocks these, your tunnel won’t form. Steps:
- Log in to your router/firewall and ensure these ports are allowed outbound and inbound for the FortiClient host.
- If you’re behind a corporate firewall, request IT to whitelist FortiGate VPN endpoints and confirm NAT-T is enabled on the gateway.
- If you’re using a VPN split-tunnel setup, confirm the correct routes are pushed when the tunnel is established.
FortiClient configuration checks
Profile correctness
- Confirm the FortiClient VPN Profile is set to use IPSec with IKEv2 or a compatible mode your gateway supports.
- If your VPN uses certificates, ensure the certificate authority (CA) certificate is trusted by Windows and the FortiClient trust store.
Authentication method compatibility
- Password-only, certificate-based, or dual-factor: make sure the selected method matches what the gateway expects.
- If multi-factor is required, ensure the MFA method is accessible and not blocked.
Phase 1 and Phase 2 settings
- IKE version: IKEv2 is common; ensure both ends support it.
- Encryption and integrity: common defaults (AES-256, SHA-256) should align with the gateway. Mismatches can fail negotiations.
NAT Traversal (NAT-T)
- NAT-T helps when users are behind NAT devices. Confirm NAT-T is enabled on both FortiClient and the gateway if you’re behind NAT.
Dead-peer detection and rekey
- If the gateway has aggressive dead-peer detection settings, a mismatch can cause drops. Adjust DPD/rekey timers if you control the gateway.
Windows 11-specific tweaks
Network Adapter settings
- Go to Control Panel > Network and Internet > Network Connections > [Your VPN Adapter] > Properties > Internet Protocol Version 4 (TCP/IPv4) > Properties.
- Ensure DNS settings don’t override VPN DNS unnecessarily; use the VPN-provided DNS if appropriate.
- Disable IP fragmentation or path MTU issues by testing with different MTU sizes (1400–1500 range). Some networks require MTU tuning for IPSec.
Service and protocol checks
- Ensure the following services are running:
- IPSec Connectivity (Policy Agent)
- Secure Socket Tunneling Protocol (Sstp) is not interfering unless you’re using it
- Disable third-party VPN clients that could conflict with FortiClient when testing.
Credential cache and certificate store
- Clear any conflicting credentials in Windows Credential Manager.
- If using certificates, ensure the certificate is installed in the Local Computer store (not just Current User) for the FortiClient service to access.
Common error codes and how to fix them
- 0x8009030c (The logon attempt failed): Recheck credentials or certificate validity; verify the server certificate chain.
- 0x80072757 (The connection attempt failed because the connected party did not respond): Check network reachability to the VPN gateway; ensure firewall isn’t blocking.
- 0xc0020017 (A connection attempt was rejected or timed out): Likely a port or policy mismatch; verify IKE ports and NAT-T.
- 50 of ESP negotiation failures: Confirm both ends support matching encryption/auth algorithms and that no firewall is inspecting IPsec packets.
Table: common causes vs fixes
| Cause | Checkpoint | Fix |
|---|---|---|
| Port blocked on router | UDP 500/4500 blocked | Open ports, enable NAT-T |
| Certificate chain invalid | CA not trusted | Import/trust CA cert on Windows |
| Time drift | Clock skew > 5 minutes | Enable NTP sync |
| DNS misconfiguration | VPN DNS overridden by local DNS | Set VPN DNS or disable split-tunnel DNS leaks |
| Software mismatch | FortiClient outdated | Update FortiClient and gateway firmware |
Step-by-step troubleshooting checklist (repeatable in under 15 minutes)
- Reboot everything and try a different network
- Update FortiClient and Windows 11
- Verify VPN server address and credentials
- Check firewall allowances and port accessibility
- Inspect FortiClient logs for IKE phase errors
- Validate NAT-T and IPsec settings on both ends
- Test with a certificate-based profile if you’re using password-based authentication
- Confirm time synchronization and certificate validity
- Clear conflicting credentials and ensure the certificate store is correct
- Re-test and document any error codes for IT support if needed
Best practices for a robust, long-term VPN setup
- Schedule regular updates for FortiClient and Windows
- Use certificate-based authentication where feasible for stronger security
- Enable MFA if your gateway supports it
- Maintain a dedicated VPN DNS setup to prevent leaks
- Periodically review firewall rules and router configurations to adapt to network changes
- Keep a local copy of commonly used VPN profiles for quick reconfiguration
Real-world scenarios and troubleshooting stories
- Scenario A: You’re at a cafe with a public Wi-Fi. IPSec negotiation fails due to captive portal. Fix: connect to a trusted network, then retry or use a mobile hotspot.
- Scenario B: Company updates its FortiGate gateway with a new cert, but Windows clients fail to trust the new CA. Fix: push updated CA certificates to all endpoints and re-import the gateway cert chain.
- Scenario C: User toggled a security setting in Windows that blocks non-Windows-signed certificates. Fix: revert to default security settings or explicitly trust Fortinet certificates.
Security considerations
- Always verify the VPN gateway’s certificate fingerprint with your IT admin before accepting a new certificate.
- Don’t disable essential security features to get a VPN working; instead, align settings and update components.
- Consider using a VPN with strong encryption, updated algorithms, and a modern handshake protocol (IKEv2 with AES-256, SHA-256, perfect forward secrecy).
Monitoring and health checks
- Use FortiClient’s built-in diagnostics to test connectivity to the VPN gateway
- Check Windows Event Viewer for relevant errors under Windows Logs > System and Application
- Maintain a simple uptime/logging dashboard for VPN success rates, outages, and common error codes
Frequently Asked Questions
What is IPSec and why is it used with FortiClient?
IPSec is a suite of protocols that secures Internet Protocol communications by authenticating and encrypting each IP packet in a data stream. FortiClient uses IPSec to provide secure, encrypted tunnels to FortiGate gateways. The Complete Guide to Uninstalling NordVPN Windows Mac: The Complete Guide to Uninstalling NordVPN Windows Mac
How do I know if my FortiClient is up to date?
Open FortiClient, go to the About or Settings section, and look for Update or Check for Updates. Ensure you have the latest compatible version for your gateway.
Which ports should be open for FortiClient IPSec?
Typically UDP 500 (IKE), UDP 4500 (NAT-T), and ESP (IP protocol 50). Some networks may require additional ports depending on the gateway configuration.
What should I do if I get error 0x8009030c?
This usually means authentication failed or the certificate is not trusted. Double-check credentials, certificate validity, and the trust chain.
How can I verify the gateway certificate on Windows 11?
Use the certificate manager (certmgr.msc) to inspect the Trusted Root Certification Authorities and Personal stores for the Fortinet certificate.
Can I use a different VPN protocol if IPSec fails?
If your gateway supports it, you can switch to IKEv2 with FortiClient or another protocol like SSL VPN, but you’ll need gateway-side support and to reconfigure the profile. How To Use NordVPN With Microsoft Edge Your Ultimate Guide: Seamless Surfing, Security, And Speed
Why does my VPN work on another device but not my PC?
This points to device-specific settings: firewall rules, outdated drivers, certificate trust store issues, or misconfigured FortiClient profile on the PC.
How important is time synchronization for IPSec?
Very important. If the device clock is off, certificates may be rejected, causing connection failures.
Should I disable antivirus to troubleshoot?
Only temporarily for testing. If a security product interferes, add FortiClient as an exception rather than turning off protection completely.
How can I improve VPN reliability long-term?
Keep software up to date, use certificate-based authentication, enable MFA, ensure NIC drivers are current, and maintain consistent network conditions with stable DNS settings.
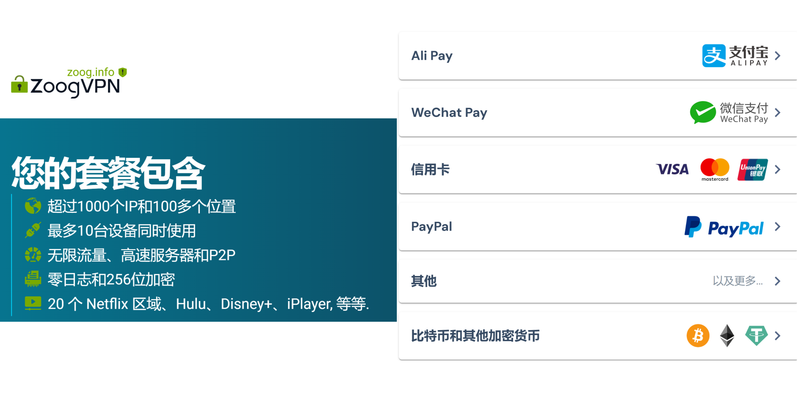
If you’ve found this guide helpful and want a smoother VPN experience, consider checking out our recommended security tools and resources. NordVPN offers a trusted path for additional protection when you’re on risky networks. Click to learn more: NordVPN Nordvpn not working in china heres exactly how to fix it
Sources:
Radmin vpn linux: 全面指南与实用技巧,提升你的VPN体验
未竟之语:人生下半场的智慧,别让遗憾成为你最后的未竟之语—— VPN 隐私保护、上网自由与安全完整指南
海外アプリをvpnでダウンロードする方法:地域制 を突破する実践ガイド
中華電信 esim 申請流程:完整教學與常見問題解答 | eSIM 申請條件、步驟、裝置支援、常見錯誤與解決方案