Is Zscaler a VPN and Whats the Difference? A Deep Dive into Zscaler, VPNs, and Secure Networking
Is Zscaler a VPN and whats the difference? Short answer: no, not in the traditional sense. Zscaler is a security platform that helps you browse, access apps, and protect data, while a VPN virtual private network creates a private tunnel for your internet traffic. They solve related problems but in different ways. In this video-ready guide, you’ll get a clear comparison, practical use cases, and actionable tips to choose what fits your needs.
Quick fact: Zscaler is not a conventional VPN, but it can provide similar privacy and access-control benefits through its cloud security services. If your goal is to secure web traffic, access internal apps, and enforce corporate policies without routing all traffic through a single company VPN, Zscaler might be the right fit. In this guide, we’ll cover:
- What Zscaler is and how it works
- How VPNs differ from Zscaler services
- Real-world scenarios where you’d use one or both
- Pros, cons, and hidden gotchas
- Tips for choosing a solution that matches your needs
- A practical checklist to decide quickly
Useful URLs and Resources text only Apple Website - apple.com Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence Zscaler Official - zscaler.com NordVPN Information - nordvpn.com Tech community discussions - reddit.com VPN comparison guides - www.techradar.com/vpn Why Your Apps Are Refusing to Work with Your VPN and How to Fix It
What is Zscaler? A quick overview
- Zscaler is a cloud-native security platform focused on secure web access, cloud‑based firewalling, data loss prevention, and threat protection. It routes user traffic to the Zscaler cloud where security policies are applied, rather than sending traffic to a traditional on-site firewall.
- Core components often used by organizations:
- Zscaler Internet Access ZIA: protects users accessing the internet.
- Zscaler Private Access ZPA: provides zero-trust access to internal apps without exposing them publicly.
- How it works in practice: when you try to reach a website or an app, your traffic is redirected to the Zscaler cloud where security checks occur before it reaches the internet or the destination app.
Is Zscaler a VPN? The best way to frame it
- Not a traditional VPN. A traditional VPN creates a secure, encrypted tunnel between your device and a VPN server, and often routes all or most of your traffic through that tunnel.
- Zscaler isn’t primarily designed to tunnel all traffic for a user. Instead, it secures and controls access to internet resources and internal apps via cloud-based security policies, with traffic often steered through its security stack as needed.
- In practice, you’ll hear terms like “Zero Trust Network Access ZTNA” when describing ZPA, which is a different security model from VPNs but serves a similar goal: secure access without exposing networks.
What’s the difference? Side-by-side basics
- Purpose
- VPN: Create a private tunnel to a server, often masking your IP and encrypting all traffic.
- Zscaler ZIA/ZPA: Enforce security policies, inspect traffic, and securely connect users to the internet and internal apps without exposing the network.
- Traffic routing
- VPN: Routes traffic through a VPN gateway, typically for all traffic or per-application traffic.
- Zscaler: Routes traffic to the Cloud security platform for inspection, with policy enforcement; ZPA enables direct access to apps without exposing them publicly.
- Privacy and visibility
- VPN: Can obscure location data and hide browsing from local networks, but can be less granular on policy enforcement.
- Zscaler: Focused on security policy enforcement, threat protection, and data loss prevention; visibility is extensive for corporate safety but not a privacy proxy.
- Deployment model
- VPN: Often requires on-prem or cloud VPN concentrators; client software to connect.
- Zscaler: Cloud-native; users connect via a lightweight client or connect through browser/app traffic with policy enforcement in the cloud.
Key benefits and where each shines
- VPNs shine when you need:
- Simple, consistent IP masking and geographic routing
- Access to a specific remote network resource as if you’re onsite
- A familiar model for remote workers and frequently used in smaller setups
- Zscaler shines when you need:
- Comprehensive web and app security with threat protection
- Granular, policy-based access control Zero Trust
- Lightweight deployment using the cloud, with less reliance on traditional VPN gateways
- Secure access to internal apps without exposing them publicly ZPA
Real-world use cases Лучшие бесплатные vpn для россии в 2026 году: полный обзор, советы и сравнение
- Remote workers who need to reach internal apps securely: ZPA can provide zero-trust access to those apps without a wide VPN tunnel.
- Teams needing web security and data protection for SaaS usage: ZIA offers threat protection, data loss prevention, and SSL inspection as a service.
- Organizations seeking simpler management and scalable security: Cloud-native Zscaler can be easier to scale than on-prem VPNs in large, global enterprises.
- Privacy-focused browsing from home: A VPN is typically better for masking location and encrypting general internet traffic, but Zscaler’s security features apply mainly to enterprise-controlled traffic.
How to compare costs and performance
- Costs can vary widely by vendor, user count, and features. In general:
- VPNs: Often priced per user or per device with predictable licensing for basic tunnels; performance depends on gateway capacity and routing.
- Zscaler: Pricing scales with the security services selected ZIA, ZPA, DLP, etc.. Cloud-based models can reduce on-prem hardware costs but require robust policy management.
- Performance considerations:
- VPNs: Performance can be impacted by the distance to the VPN gateway and the gateway’s load; some services offer split tunneling to improve speed.
- Zscaler: Performance hinges on cloud route optimization, local internet breakouts, and how effectively traffic is steered to Zscaler data centers. Latency can be a factor if the closest data center isn’t optimal for a given user location.
Security and privacy considerations
- VPN:
- Pros: Strong encryption for data in transit, can hide your IP from local networks.
- Cons: Does not inherently inspect encrypted traffic unless combined with other tools; sharing one VPN gateway for many users can create a single point of failure.
- Zscaler:
- Pros: Deep security inspection, zero trust access to apps, granular policy enforcement, data loss prevention, and threat protection.
- Cons: Primarily designed for enterprise security; may not function as a user’s general privacy proxy for all internet activities.
- Privacy implications:
- VPNs can log data depending on the provider; some offer no-logs policies; free VPNs often log more data.
- Zscaler logs are typically used for security and compliance within a corporate policy framework; privacy concerns are generally focused on enterprise users’ data control and monitoring rather than public internet anonymity.
Implementation considerations and migration tips
- If you’re moving from VPN to Zscaler ZIA/ZPA:
- Start with a pilot in one department to map apps, traffic flows, and policy needs.
- Define zero-trust access rules for internal apps ZPA and security policies for internet usage ZIA.
- Plan for break-glass procedures and incident response scenarios.
- If you’re adding VPN alongside Zscaler:
- Decide if you’ll route all traffic through VPN or use split tunneling for certain resources.
- Ensure compatibility with Zscaler’s traffic inspection and avoid conflicts in firewall rules.
- Common pitfalls:
- Overly broad policies that degrade user experience.
- Underestimating the need for ongoing policy tuning and user education.
- Under-protecting internal apps during transition—make sure ZPA access is properly configured.
Integration with other security tools
- Zscaler integrates with SIEMs, SOAR platforms, and identity providers IdP to enforce access and security policies.
- VPNs can also integrate with enterprise security stacks, but you may need additional tooling for secure access to internal apps that ZPA provides.
- Example workflows:
- User authenticates via SSO to access internal apps through ZPA.
- ZIA inspects outbound web traffic and enforces data protection policies.
- Security teams receive alerts and respond via SIEM/SOAR integrations.
Best practices for optimizing your setup Windscribe vpn extension for microsoft edge a complete guide 2026: Boost Edge Security, Speed, and Privacy
- Start with a clear policy framework:
- Define who can access what, from where, and under which conditions.
- Separate policy layers for ZPA internal apps and ZIA internet access.
- Use local internet breakouts where possible:
- This reduces latency by serving content from the nearest cloud region.
- Implement robust identity management:
- Enforce MFA and strong identity checks for access to internal apps.
- Regularly review and adjust policies:
- Schedule quarterly reviews or after major workload changes.
- Educate users:
- Communicate how access works, what to expect, and how to report issues.
A practical comparison checklist
- What’s your primary objective?
- If you need secure internet access and app protection, consider ZIA/ZPA.
- If your main goal is to mask IPs or access a private network, a VPN may be simpler.
- Do you require zero-trust access to internal apps?
- Yes: ZPA is a strong fit; no traditional VPN required.
- No: A VPN could suffice for basic remote access needs.
- What-level of traffic inspection do you need?
- Full threat protection and data loss prevention: ZIA with ZPA.
- Basic encryption and access: VPN can be adequate.
- What’s your deployment model?
- Cloud-native, scalable: Zscaler wins.
- On-prem or hybrid with existing VPN gateways: You might keep or layer VPNs.
- How critical is latency for your users?
- Use local internet breakouts and cloud routing with ZIA/ZPA where possible.
What to look for in a vendor comparison
- Coverage: Does the provider protect web, app access, and data across your user locations?
- Policy granularity: Can you carve precise access rules for different groups and apps?
- Cloud footprint: Are data centers close to your users to minimize latency?
- Compliance and reporting: Are there robust audit trails and compliance features?
- Vendor support and ecosystem: Is there strong customer support, partner integrations, and a healthy ecosystem?
Table: Quick feature comparison VPN vs Zscaler ZIA/ZPA
- VPN
- Traffic model: Tunnels, often all traffic
- Security features: Basic, depends on gateway; may require extra tooling
- Access model: Network-focused, sometimes broad access
- Deployment: On-prem or cloud gateways
- Suitable for: Simple remote access, basic privacy needs
- Zscaler ZIA/ZPA
- Traffic model: Policy-driven routing to cloud security platform
- Security features: Layered security, threat protection, DLP, SSL inspection
- Access model: Zero Trust to apps; minimal exposure
- Deployment: Cloud-native, scalable
- Suitable for: Enterprises needing strong security, app access control, and cloud integration
Frequently asked questions
Is Zscaler a VPN?
No. Zscaler provides cloud-based security services ZIA for internet security and ZPA for secure access to internal apps rather than a traditional VPN tunnel. How much does letsvpn really cost a real look at plans value and comparable options
How does ZPA differ from a VPN?
ZPA uses zero-trust principles to grant access to specific internal apps without exposing the entire network, while a VPN creates a tunnel that might give broader network access.
Can Zscaler replace my VPN entirely?
For many enterprises, yes, especially for secure access to internal apps and web security. Some organizations keep VPNs for legacy reasons or for specific workflows, so a hybrid approach is common during transition.
Is ZIA part of Zscaler’s security stack?
Yes. ZIA is Zscaler Internet Access, focusing on secure web access and internet traffic inspection.
Do I need to install software on my devices to use Zscaler?
Often a lightweight client or browser-based policy is enough, but some deployments may require a client for ZPA or deeper inspection.
How does Zero Trust work in Zscaler?
Zero Trust means you’re not trusted by default; access is granted only to verified apps or resources after authentication and policy checks. Cant connect to work vpn heres how to fix it finally
What about data privacy with Zscaler?
Zscaler logs are used for security and compliance within enterprise contexts. Privacy considerations focus on how data is monitored and protected by corporate policies.
How can I measure performance after migration?
Track latency, access times to internal apps, user satisfaction, security incident frequency, and SLA compliance with your security stack.
What are common migration mistakes?
Overly broad policies, underestimating the need for policy tuning, failing to train users, and not planning for incident response during transition.
Should I consider a hybrid VPN + Zscaler approach?
If you have legacy apps or regulatory requirements needing VPN, a hybrid approach can help bridge gaps while you migrate to ZPA/ZIA, maintaining security while not disrupting productivity.
How do I start a proof of concept POC for Zscaler?
Identify a pilot group, map all required apps and traffic, configure ZIA and ZPA test policies, run parallel security controls, and measure performance, user experience, and policy effectiveness over a set period. Fortigate ssl vpn your guide to unblocking ips and getting back online
Are there notable limitations to Zscaler?
No single solution fits all: the success of Zscaler depends on proper policy configuration, cloud connectivity, and ongoing management. Some advanced network scenarios may still require VPNs or additional tooling.
What’s a good rollout timeline?
- Week 1–2: Stakeholder alignment, goals, and pilot scope
- Week 3–6: Policy design for ZIA/ZPA, identity integration, initial rollout
- Week 7–10: Wider deployment, training, and optimization
- Week 11–12: Review, adjust, and plan for full scale
How much training do IT teams need?
Moderate training on policy design, cloud security concepts, identity integration, and incident response planning is recommended. Expect a learning curve with ongoing optimization.
How do you handle SSL inspection in ZIA?
SSL inspection is part of ZIA’s security stack, typically configured via policy to balance security needs with performance and privacy considerations, ensuring compliance with regulatory requirements.
Can end users bypass Zscaler features?
By design, policy enforcements prevent unauthorized access. Break-glass or emergency access procedures should be in place for legitimate needs, with proper auditing.
What are the best practices for securing data with Zscaler?
- Enforce data loss prevention DLP policies
- Use encryption and TLS inspection where appropriate
- Apply granular access controls and MFA
- Maintain robust logging and alerting
- Regularly audit and update security policies
You’re ready to decide Is Zscaler a VPN and whats the difference? It’s not a VPN in the traditional sense, but it can cover many of the same goals—secure access, privacy in enterprise terms, and robust threat protection—through a cloud-native, zero-trust architecture. If you’re weighing a transition from a traditional VPN to a more modern security posture, Zscaler provides a compelling path with ZIA for internet security and ZPA for app access. Use this guide as your quick-start roadmap, and tailor it to your organization’s size, regulatory needs, and user experience goals. Google Gemini and VPNs: Why It's Not Working and How to Fix It
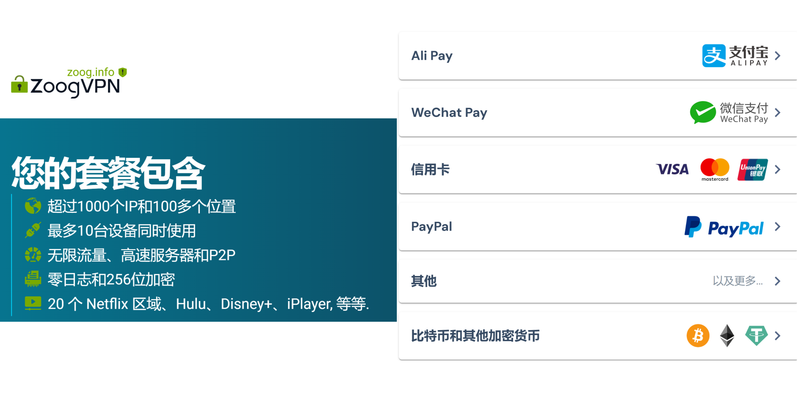
Remember: the best choice isn’t just about a feature list. It’s about how well the solution fits your workflows, how easy it is to manage, and how it scales as you grow. If you’re curious to explore concrete options and real-world setups, check out the NordVPN link for a different angle on remote access and privacy, but keep in mind Zscaler’s enterprise-focused capabilities when planning for long-term security architecture.
Frequently Asked Questions
- Is Zscaler a VPN?
- How does ZPA work without a VPN tunnel?
- What is the main difference between ZIA and VPN?
- Can Zscaler replace my firewall?
- Is Zscaler suitable for small businesses?
- How do you migrate from VPN to Zscaler?
- What are the core components of Zscaler?
- How do I ensure user privacy with Zscaler?
- What are zero-trust concepts in practice?
- How is SSL inspection managed in ZIA?
If you’d like to see more, I’ve got a deep dive coming up that breaks down real-world deployment steps, migration pitfalls, and exact policy templates you can copy for your own setup. And if you’re exploring alternative privacy and remote-access options, consider checking out the NordVPN route we mentioned earlier for a different perspective on remote access and privacy.
Sources:
Is vpn safe for gsa navigating security for federal employees and beyond
Cuanto cuesta mullvad vpn tu guia definitiva de precios: todo lo que necesitas saber sobre tarifas, planes y ahorro 2026년 중국 구글 사용 방법 완벽 가이드 purevpn 활용법
2026年款最佳华硕路由器vpn推荐与设置指南与相关优化
个人 如何 申请 vpn
Atlas vpn sul chrome web store la tua guida completa per sicurezza e privacy