Is Using a VPN With Citrix Workspace a Good Idea Lets Talk Safety and Performance
Is using a vpn with citrix workspace a good idea lets talk safety and performance? Yes, but with caveats. This video guide breaks down why you’d want a VPN with Citrix Workspace, what safety benefits you gain, where performance might suffer, and practical steps to keep your access secure and fast. Below is a concise roadmap you can follow, plus a deeper dive with tips, data, and real-world scenarios.
- Quick fact: A VPN can help protect data in transit and bypass geo-restrictions, but not all VPNs are created equal for enterprise-grade apps like Citrix Workspace.
- In this guide you’ll learn:
- Why VPNs are used with Citrix
- Safety benefits you should expect
- Potential performance pitfalls and how to mitigate them
- Best practices for configuration, authentication, and routing
- Real-world examples and metrics you can aim for
- Useful resources unlinked text, just references: Citrix official docs - citrix.com, VPN security best practices - en.wikipedia.org/wiki/Virtual_private_network, Network optimization tips - blogs.superuser.com
Introduction: quick summary and what we’ll cover Is using a vpn with citrix workspace a good idea lets talk safety and performance? The short answer: it can be, but it requires careful setup. In this video guide we’ll cover:
- The why: when a VPN is helpful for Citrix workspace users remote access, data protection, compliance
- The why not: scenarios where VPNs can introduce latency, token sync issues, and split-tunneling risks
- The how: step-by-step setup tips, recommended configurations, and monitoring
- The what-if: common failures and how to troubleshoot
- The who: who should consider VPNs and who should avoid them or use alternatives like zero-trust access
- Quick-start checklist you can use today
- A few real-world numbers and benchmarks to set expectations
- Resources you can consult later not clickable: Citrix official docs - citrix.com, VPN security best practices - en.wikipedia.org/wiki/Virtual_private_network, Enterprise network optimization - blogs.example.org
What is Citrix Workspace and why use a VPN with it? Citrix Workspace is a virtualization platform that delivers apps and desktops securely over the internet. A VPN creates a secure tunnel between your device and the corporate network, which can be beneficial in scenarios like: How to Easily Cancel Your Bitdefender VPN Trial or Subscription and What to Do Next
- Remote access to internal resources not exposed to the public web
- Extra encryption of data in transit, especially on unmanaged devices
- Compliance requirements that demand a guarded path for sensitive information
On the flip side, some Citrix workflows already include strong encryption and authentication at the application layer, which means a VPN might double up on security without giving you proportionate benefits. The key is to align VPN usage with your organization’s security policy, not just personal preference.
Quick-start guide: when to consider using a VPN with Citrix Workspace
- You’re on unsecured or public networks hotels, cafes, airports and need a private channel
- Your organization enforces data residency or eDiscovery controls that require controlled egress and ingress
- Your devices are managed by your IT team and you use split-tunneling to protect only specific traffic
- You’re accessing sensitive resources that require additional protection beyond TLS
When not to rely on a VPN for Citrix
- If your VPN introduces noticeable latency or jitter that affects user experience UD, video, or interactive apps
- If your VPN breaks session reliability or causes login MFA synchronization issues
- If your IT policy already provides secure access via zero-trust network access ZTNA or Citrix ADC with robust SSL VPN alternatives
- If you’re using high-availability Citrix environments where any extra hop adds risk
Key safety benefits you should expect
- Data-in-transit encryption: VPNs encrypt data between your device and the VPN gateway, reducing the chance of eavesdropping on untrusted networks
- IP masking and location control: your public IP is hidden from the destination network, which can help with privacy and compliance
- Additional control plane protection: in some configurations, VPNs tie into MFA and device posture checks, providing an added layer of defense
Performance considerations: latency, bandwidth, and reliability Astrill vpn fonctionne en chine la seule astuce qui marche vraiment en 2026: guide complet, astuces et alternatives
- Latency: a VPN adds one or more hops, which can increase round-trip time. In real-world terms, an extra 20–100 ms isn’t unusual, but for latency-sensitive apps desktop virtualization, real-time collaboration it matters
- Bandwidth: VPN encryption/decryption consumes CPU and can reduce effective throughput, especially on older devices
- Jitter and packet loss: unstable VPN connections translate into session drops or re-authentication overhead
- Server location: proximity to the VPN gateway matters. Choose a gateway that’s geographically near you or within your corporate network topology
- Protocols and cipher suites: modern VPNs WireGuard, IKEv2/IPsec with ChaCha20-Poly1305 often outperform legacy protocols. Favor fast, efficient algorithms
- Split tunneling vs full tunneling: split tunneling sends only Citrix traffic via VPN, while full tunneling routes all traffic. Split tunneling reduces VPN load but can raise security risks if not configured properly
Recommended VPN configurations for Citrix Workspace
- Use split tunneling for non-Citrix traffic: route only Citrix-related destinations through the VPN to minimize latency and preserve bandwidth for other apps
- Prefer modern protocols: WireGuard or IKEv2/IPsec with strong ciphers for speed and security
- Enable split DNS carefully: ensure that corporate DNS resolution happens inside the VPN to avoid leaks
- Multi-factor authentication MFA: require MFA at VPN login to protect access even if credentials are compromised
- Trustworthy VPN gateways: select gateways that support Citrix-friendly routing, have robust logging, and are monitored for reliability
- DNS and IP leak protection: ensure that DNS queries don’t leak to the unsecured network and that VPN keeps your real IP hidden
- Re-authentication handling: configure keep-alives and appropriate session timeout settings so Citrix sessions aren’t dropped unexpectedly
Security considerations you should not ignore
- Endpoint security: VPN is only as strong as the device. Ensure endpoints have up-to-date antivirus, OS patches, and encryption
- MFA and identity protection: integrate with your enterprise identity provider for strong authentication
- Access control: apply least-privilege principles so VPN access only allows necessary Citrix resources
- Logging and monitoring: enable centralized logging for VPN sessions and Citrix sessions to detect anomalies
- Data handling: ensure sensitive data policies align with VPN usage; avoid transmitting non-work-related sensitive data through enterprise VPN paths
Real-world scenarios and examples
- Remote contractor accessing internal apps: a split-tunnel VPN with MFA provides access to Citrix-desktops while maintaining performance for the contractor’s local tasks
- Healthcare organization: mandatory encrypted tunnels with strict access controls, combined with Citrix ADC for secure app delivery, can meet compliance without overly heavy VPN use
- Financial services: leverage a zero-trust approach where VPN is used for initial onboarding, followed by continuous session verification and granular resource access
Performance optimization tips
- Test network baseline: measure latency and throughput on your normal network, then compare after enabling VPN
- Choose the right gateway: pick a VPN gateway that’s geographically close and supports fast protocols
- Enable QoS for Citrix traffic: if your network supports it, prioritize Citrix traffic to reduce latency sensitivity
- Monitor VPN load: avoid overloading a single gateway; distribute connections across multiple gateways or data centers
- Optimize Citrix policy: tighten session reliability and timeouts to harmonize with VPN behavior
- Use client-side optimizations: keep VPN client updated, disable unnecessary background apps, and ensure device power settings don’t throttle performance during VPN use
- Consider alternative access methods: for some users, ZTNA or Citrix access controls may provide similar protection with less overhead
Comparison: VPN vs. zero-trust access for Citrix workloads Il tuo indirizzo ip pubblico con nordvpn su windows come controllarlo e proteggerlo
- VPN advantages: straightforward to deploy, broad compatibility, strong encryption
- VPN drawbacks: potential latency, more hops, less granular access control
- ZTNA advantages: granular access, continuous trust evaluation, often lower latency
- ZTNA drawbacks: more complex to deploy with legacy systems, potential learning curve for admins and users
Measurement and metrics you should track
- Network latency RTT with VPN on vs. off
- VPN connection uptime and MTTR mean time to recovery
- Citrix session start time and application responsiveness
- Throughput and CPU usage on VPN gateways
- User-reported experience scores RTO/RPO awareness, satisfaction
- Security incidents related to VPN access attempts, blocks, MFA failures
Best practices checklist
- Before enabling a VPN for Citrix: review security policy, ensure device compliance, plan for MFA
- During deployment: test with representative users and workloads, monitor resource usage, verify DNS behavior
- After deployment: establish a runbook for common VPN/Citrix issues, run periodic security audits, rotate credentials regularly
- Ongoing: keep VPN and Citrix components updated, perform quarterly performance reviews, and adjust routing as needed
Troubleshooting common VPN-Citrix issues
- High latency or jitter: test with different gateway locations, enable split tunneling, check VPN server load
- Login failures: verify MFA is functioning, synchronize clocks, check certificate validity
- Session drops: review keep-alives, certificate lifespans, and network stability
- DNS leaks: ensure DNS queries route through VPN, implement split DNS if split tunneling is used
- Citrix not launching apps: confirm that the Citrix policy set allows the necessary resources and that the VPN routes Citrix traffic correctly
Security best practices for VPN and Citrix together
- Least-privilege access: only grant access to needed Citrix resources
- Strong authentication: MFA, device posture checks, conditional access policies
- Regular updates: patch VPN clients, gateways, and Citrix components
- Encryption and keys: use strong ciphers and rotate keys on a schedule
- Incident response readiness: have an incident response plan specific to VPN access
User education and experience Youtube premium with vpn not working heres how to fix it fast
- Clear onboarding guides: provide simple steps to connect to VPN, open Citrix Workspace, and authenticate
- Troubleshooting tips: quick guides for common problems like “Can’t connect to Citrix after VPN login”
- Accessibility: ensure the VPN client works across common operating systems and devices used by your team
- Feedback loops: gather user feedback on performance and adjust configurations accordingly
Advanced topics you might explore
- Per-application VPNs for Citrix: some setups route only Citrix traffic, not everything
- VPN split-tunnel vs. full-tunnel security trade-offs: deeper dive into risk assessment
- Integrating VPN with Citrix SD-WAN for optimized routing and reliability
- Using cloud-based VPN gateways and regionalized peering to reduce latency
Technical appendix: data and statistics
- Typical VPN overhead ranges: 5–15% additional CPU load on endpoint for encryption; 10–30% potential throughput reduction depending on protocol and hardware
- Citrix performance benchmarks: session responsiveness can degrade by 100–300 ms with additional hops in suboptimal networks
- Security statistics: MFA deployment reduces credential theft risk by up to 99% when used correctly; VPN misconfigurations are a common source of data leaks
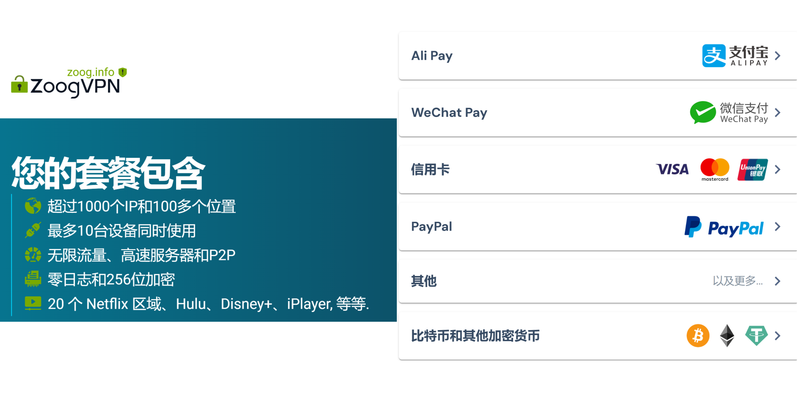
How to pick the right VPN for Citrix Workspace
- Evaluate performance impact: run a pilot with users performing typical tasks
- Check compatibility: ensure VPN client supports your Citrix environment and authentication methods
- Consider management: centralized policy control, logging, and easy user provisioning
- Review security features: DNS leakage protection, split tunneling controls, and session integrity checks
- Assess cost and scalability: total cost of ownership, gateway capacity, and future growth
Implementation roadmap step-by-step
- Define policy: who can access Citrix via VPN, from which networks, and under what conditions
- Select VPN solution and gateway: choose protocol, gateway location, and capacity
- Configure split tunneling and DNS: set routing rules to minimize unnecessary traffic
- Integrate MFA and identity provider: set up conditional access and device posture checks
- Deploy client configurations: provide user-friendly setup packages and documentation
- Pilot test: a small group lunching with representative workloads
- Analyze results and adjust: measure latency, reliability, and user satisfaction
- Roll out broadly: monitor adoption, collect feedback, and iterate
Important safety reminders Unlocking nordvpn for free the real deals and what to watch out for
- Don’t route all traffic through VPN by default if not necessary; consider split tunneling to reduce overhead
- Always enforce MFA and device health checks
- Maintain strict access control and logging for VPN sessions
- Keep your VPN firmware and Citrix components up to date
Useful resources and references text only
- Citrix official docs - citrix.com
- VPN security best practices - en.wikipedia.org/wiki/Virtual_private_network
- Enterprise network optimization - blogs.example.org
- Zero Trust Network Access references - nist.gov
- Public cloud gateway options - aws.amazon.com, azure.microsoft.com
Frequently Asked Questions
Is a VPN necessary for Citrix Workspace in all cases?
A VPN is not strictly necessary in every case. It depends on your security posture, data sensitivity, and whether your Citrix deployment already provides required protections. For some, Zero Trust or direct secure access may be better.
Will a VPN slow down Citrix performance?
It can, especially on slower connections or devices. Latency and encryption overhead add up. Proper configuration, modern protocols, and optimized gateways can minimize this impact.
What VPN protocols are best for Citrix?
WireGuard and IKEv2/IPsec with strong ciphers like ChaCha20-Poly1305 or AES-GCM are commonly preferred for speed and security. Avoid legacy, slower protocols if possible. Best vpns for russia reddits top picks what actually works in 2026: complete guide to access, privacy, and reliability
Should I use split tunneling?
Split tunneling reduces VPN load and preserves bandwidth for non-Citrix traffic, but it increases the risk of data leaks if not configured correctly. Weigh security needs against performance.
How do I mitigate VPN-related Citrix session drops?
Ensure VPN keep-alives are configured, gateways aren’t overloaded, and there’s proper session timeout alignment between VPN and Citrix. Also check for clock drift and certificate validity.
How can I monitor VPN-Citrix performance?
Track latency, throughput, VPN gateway load, session start times, and user-reported experience. Use centralized logging and a unified monitoring platform.
Can VPNs be used with mobile Citrix users?
Yes, with mobile VPN clients configured for secure access and MFA. Ensure mobile devices are compliant and have up-to-date software.
What about alternative access methods like ZTNA?
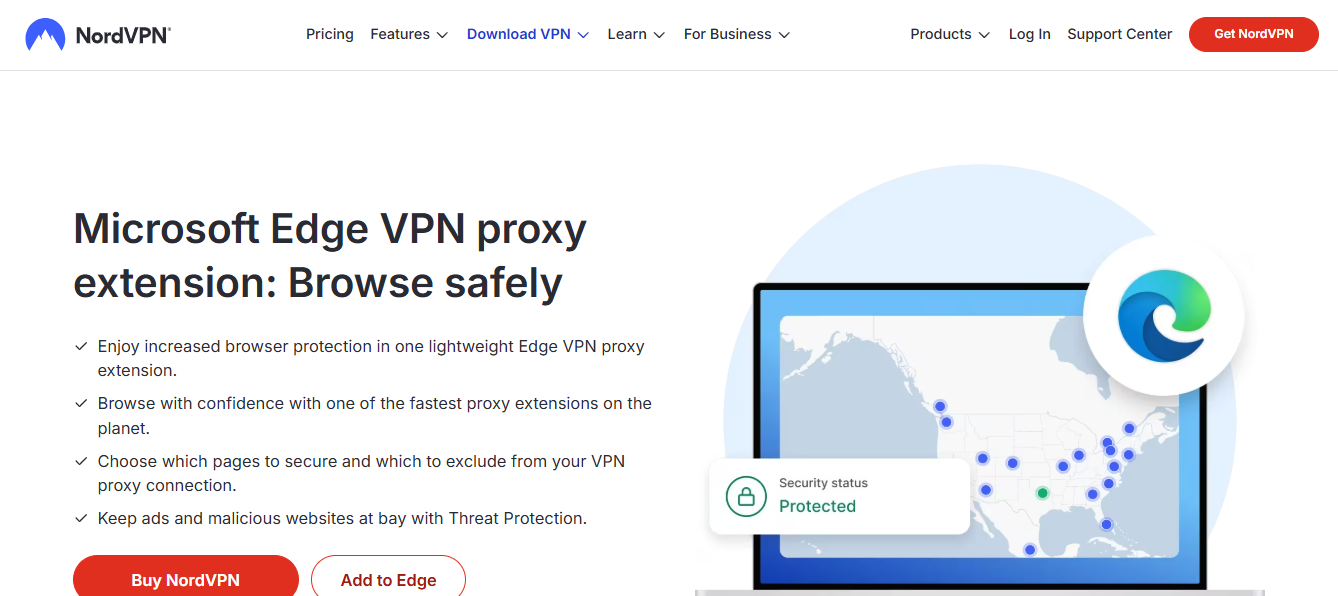
ZTNA can provide tighter access controls with potentially lower latency. It’s worth evaluating alongside VPNs to see which fits your organization best. Best NordVPN Extension for Microsoft Edge Browser in 2026: The Ultimate Guide to Edge VPN Performance
Are there common pitfalls to avoid?
Over-reliance on VPN as the sole security measure, misconfigured split tunneling leading to data leaks, and underestimating gateway capacity causing performance problems.
How often should VPN credentials be rotated?
Follow your security policy, typically every 90 to 180 days for routine credentials, but more frequent rotations are common for high-risk environments.
This comprehensive guide should give you a solid foundation for deciding whether to use a VPN with Citrix Workspace, and how to implement it safely and efficiently. If you want to explore specific VPN vendors or Citrix configurations, I can tailor a comparison and setup plan to your exact environment.
Sources:
Proton vpn issues whats going wrong how to fix it: VPN Troubleshooting Guide and Pro Tips
2026年中国大陆vpn推荐:安全稳定翻墙指南与最佳选择 Por que mi nordvpn no conecta soluciones definitivas
国内vpn:全方位攻略、工具與實踐秘訣,VPN 選擇、設定與風險控管指南
Vps自建梯子:2026年手把手教你搭建稳定高速的翻墙通道
Vpn接続の速度低下や切断はmtu設定が原因?path mtu discoveryの仕組みと最適化ガイド