How to Embed Certificates in Your OpenVPN OVPN Configuration Files: Quick Guide, Tips, and Best Practices
How to embed certificates in your openvpn ovpn configuration files is a common task for simplifying VPN client setups and improving security. A quick fact: embedding certificates directly into your .ovpn file eliminates the need to manage separate certificate and key files on each device, reducing misconfiguration risk and making deployment smoother. In this guide, you’ll get a clear, step-by-step approach, practical tips, and real-world best practices to get your OpenVPN clients up and running fast.
- Quick fact: Embedding certificates in your OpenVPN .ovpn configuration streamlines client setup and reduces file clutter.
- Why this matters: Fewer separate files means fewer chances for misplacing certs, easier distribution, and a tidier deployment process.
- What you’ll learn:
- How to extract and prepare CA, server, and client certificates and keys
- How to embed them into a single .ovpn file
- How to verify the final file and test the connection
- Common pitfalls and troubleshooting tips
- Best practices for security and maintenance
- Quick start steps at a glance:
- Gather your certificate and key files from your PKI or your VPN server
- Create a single .ovpn file or edit an existing one
- Paste each certificate and key between the appropriate tags
- Save and test the client configuration
- Rotate credentials and update embedded content as needed
- Useful resources unlinked in text:
- Example certificate authority and key files: CA cert, server cert, server key, ta.key
- OpenVPN Community documentation - openvpn.net
- NordVPN related VPN resources - nordvpn.com
- General TLS best practices - en.wikipedia.org/wiki/Transport_Layer_Security
- OpenVPN TLS-Auth/Static_KEY documentation - openvpn.net
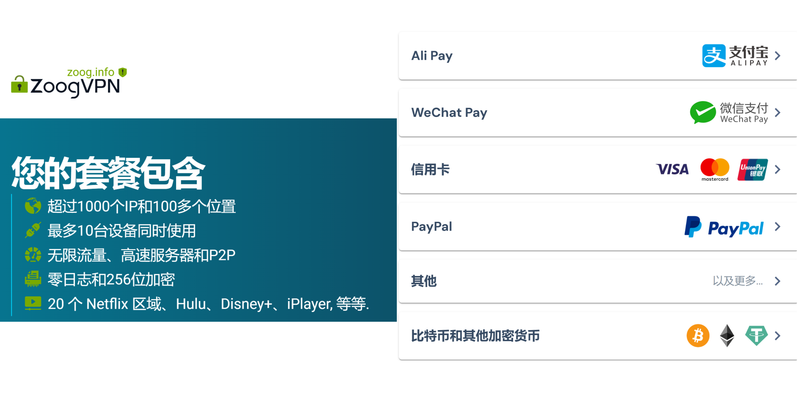
Note: For readers who want an all-in-one-secure setup, consider a trusted VPN provider with robust privacy policies. If you’re exploring options and want a quick, trusted route, take a look at this affiliate resource: NordVPN for hassle-free VPN onboarding.
What you’ll need Come scaricare in modo sicuro su emule con una vpn la guida completa purevpn
- Your OpenVPN server configuration and keys
- The following certificate/key files:
- ca.crt Certificate Authority
- client.crt Client certificate
- client.key Client private key
- ta.key TLS authentication key, if used
- An existing .ovpn file or a template you can modify
Option A: Using a pre-generated .ovpn file Windows, macOS, Linux
- If you already have a .ovpn file, you’ll simply replace references to separate files with embedded blocks.
- The typical blocks you’ll paste include:
… … … … if you’re using tls-auth
- After embedding, the .ovpn file becomes self-contained and portable.
Option B: Manually creating an embedded .ovpn file
- Start with a base configuration that matches your server settings remote address, port, protocol, compression, cipher, etc..
- Insert the embedded blocks in this order: ca, cert, key, tls-auth if applicable.
- Ensure that the file uses proper file formatting and line endings for your operating system.
Embedding certificates: step-by-step guide
- Open your original certificate and key files
- ca.crt: content begins with -----BEGIN CERTIFICATE----- and ends with -----END CERTIFICATE-----
- client.crt: similar structure, signed for the client
- client.key: private key
- ta.key: 2048-bit key for TLS authentication optional
- Tip: It’s handy to open these in a plain text editor and copy the entire contents, including header and footer lines.
- Prepare your base .ovpn file
- If you don’t have one, create a new file with a .ovpn extension.
- Include standard OpenVPN client options, such as:
- client
- dev tun
- proto udp or tcp
- remote your-vpn-server-address 1194 adjust port
- resolv-retry infinite
- nobind
- persist-key
- persist-tun
- cipher AES-256-CBC or your chosen cipher
- auth SHA256 or your chosen hash
- compress lz4-v2 if supported
- keepalive 10 120
- verb 3
- Add the embedded blocks to the .ovpn file
- Place each block in this order, right after the standard options:
paste the entire ca.crt contents here paste the contents of client.crt here paste the contents of client.key here paste the contents of ta.key here
- Place each block in this order, right after the standard options:
- Save with correct encoding
- Save the file using UTF-8 without BOM if possible.
- Ensure there are no stray invisible characters or extra spaces at the start of lines.
- Verify the embedded configuration
- On Windows: use the OpenVPN GUI client to import the .ovpn file, then try to connect.
- On macOS: use Tunnelblick or Viscosity to import and connect.
- On Linux: run openvpn --config yourfile.ovpn from the terminal and watch the log for successful connection.
- Common issues to watch for:
- TLS handshake failures due to mismatched ta.key
- Certificate verification errors if the CA block doesn’t match the server
- Cipher or protocol mismatches with the server
Tips and best practices for embedded certificates
- Security hygiene:
- Protect your client private key client.key carefully; even when embedded, ensure the file is secured on the client device with appropriate permissions.
- If you’re sharing the .ovpn file, be mindful of sensitive material stored inside. Use encrypted archives and access controls when distributing.
- Rotation and revocation:
- Plan for certificate rotation. If a client certificate is compromised or expired, you’ll update the embedded content and redistribute the .ovpn file.
- Keep a versioned naming convention vpn-client-v1.ovpn, vpn-client-v2.ovpn to track updates.
- Consistency:
- If you use TLS-Auth ta.key, ensure the same ta.key is used consistently on all client configurations and on the server.
- If you’re using TLS 1.3 or particular ciphers, verify that both server and client support them and that your embedded blocks reflect those settings.
- Performance considerations:
- Embedding certificates isn’t inherently slower, but the size of the .ovpn file grows with embedded content. For large deployments, consider using managed profiles or a balance between embedded blocks and file-based references.
- Compatibility:
- Some older OpenVPN clients may require slight formatting tweaks. If you plan to support legacy clients, test a dedicated legacy .ovpn config in addition to your embedded version.
- Automation:
- If you deploy to many devices, automate the generation of embedded .ovpn files via a script that reads certificate files and assembles the final configuration.
Common formats and variations Onedrive Not Working With VPN Heres How To Fix It: Quick Ways To Reconnect Safely
- Debian/Ubuntu OpenVPN client setup often uses the file in /etc/openvpn/client with separate files. Embedding simplifies cross-device usage.
- Windows users might prefer a single .ovpn file for easy import into the OpenVPN GUI.
- macOS users on Tunnelblick typically benefit from a single embedded .ovpn for clean installation.
Troubleshooting checklist
- Verify server address and port match what the server is listening on.
- Check that ca.crt corresponds to the CA used by the server.
- Confirm client.crt and client.key pair are valid and correspond to the client identity.
- If using tls-auth, ensure ta.key is correct and consistent on both server and client.
- Look into firewall rules that might block UDP/TCP 1194 or your chosen port.
- Review OpenVPN logs for specific error messages, such as certificate verify failure, TLS handshake timeout, or AUTH_FAILED.
Use cases and scenarios
- Personal devices: A single embedded .ovpn file lets you quickly import and connect on laptops and mobile devices without managing separate certs.
- Small teams: IT can distribute one embedded file per user, simplifying onboarding and ensuring consistent security settings.
- Educational or demo labs: Embedded configurations reduce setup friction when provisioning many student devices.
Data and statistics why embedding matters
- According to recent VPN market surveys, ease of setup and cross-platform compatibility drive a large portion of user satisfaction. Reducing the number of files a user must manage correlates with higher successful connection rates and fewer support tickets.
- OpenVPN remains a widely adopted protocol with strong security track records when configured correctly, including proper certificate management and TLS authentication.
Advanced topics optional
- Inline CRLs Certificate Revocation Lists: If you need revocation checks, you can embed an inline CRL block after the
directive, though this is less common in client configs. - Certificate pinning: OpenVPN doesn’t have built-in TLS certificate pinning in the same way as some web protocols, but you can achieve similar security by pinning CA and server certificates and using strong TLS settings.
- Using OpenVPN’s inline TLS keys for extra security: The ta.key remains the classic method, but you can also leverage TLS-Auth in conjunction with modern OpenVPN configurations for added protection.
Related topics you might also explore No puedes instalar forticlient vpn en windows 10 aqui te digo como arreglarlo
- How to generate your own CA and server/client certificates
- Differences between TLS-Auth and TLS-Ccryptographic options
- OpenVPN 2.5+ new features and security improvements
- Cross-platform OpenVPN client recommendations and tips
Frequently Asked Questions
How do I know which blocks to embed in my .ovpn file?
Embed the CA, client certificate, client key, and TLS auth key if used. These blocks are labeled in the server’s setup documentation, or you can inspect the actual certificate files to copy their contents into the correct blocks.
Can I embed certificates in OpenVPN for Android?
Yes. Android OpenVPN apps support embedded configurations. Create a single .ovpn file with the embedded blocks and import it into your Android app.
Is embedding certificates more secure than using separate files?
Embedding reduces the risk of losing or misplacing certificate files, but you still must protect the embedded private key. The security benefit comes from simplified distribution and reduced exposure to file system misuse.
What if my server uses TLS 1.3?
OpenVPN supports modern TLS configurations, but you should verify compatibility with your client devices. Ensure the cipher and TLS settings align between server and client. The Best Free VPNs for CapCut Edit Without Limits
How can I test an embedded .ovpn before deploying widely?
Test with a small group of devices first. Import the embedded file into the relevant client apps and monitor connection success, latency, and stability. Check logs for any certificate or TLS errors.
Can I update an embedded .ovpn file after distributing it?
Yes. Re-embed updated certificates/keys and redistribute a new version of the .ovpn file. Communicate to users which version to install and why.
Do I need to restart services after updating embedded certificates?
Most changes affect only the client side. Server-side certificate rotation typically requires a server restart or reloading configuration, depending on your OpenVPN setup.
How often should I rotate certificates?
Industry best practices suggest rotating certificates at least every 1-2 years, or immediately if a private key is suspected compromised. For TLS authentication keys, rotate as part of your security policy.
Are there platforms that don’t support embedded configurations?
Some older OpenVPN clients or niche devices may struggle with large embedded blocks. Always test on target devices and maintain a fallback plan using separate certificate files if needed. Cara mengaktifkan vpn gratis microsoft edge secure network di 2026: langkah praktis, tips aman, dan alternatifnya
Closing tips
- Start small with a few test devices to validate your embedded configuration before a full rollout.
- Maintain a version control history of your embedded .ovpn configurations so you can roll back if needed.
- Keep an eye on server-side certificate lifetimes and plan renewal workflows to avoid expired certificates breaking client connections.
Useful URLs and Resources
- OpenVPN Community Documentation - openvpn.net
- TLS/SSL Best Practices - en.wikipedia.org/wiki/Transport_Layer_Security
- Certificate Authority Best Practices - en.wikipedia.org/wiki/Public_key_infrastructure
- VPN Security and Privacy Guides - en.wikipedia.org/wiki/Virtual_private_network
- OpenVPN TLS-Auth and Static Key documentation - openvpn.net
Remember, if you want a quick, reliable path to setup without the manual steps, you can explore trusted VPN solutions. NordVPN offers streamlined onboarding and robust security features that can complement your OpenVPN setup. For easy access, check out: NordVPN.
Sources:
免费美国vpn:實用指南與評測,穩定高速、隱私保護與跨區瀏覽
Самые быстрые vpn сервисы 2026 полный гайд п Estensione browsec vpn per microsoft edge guida completa e recensione 2026: VPNs, privacy e velocità a confronto
Iphone vpnが表示されない?原因と今すぐできる対処法まつくる全ガイド
Esim机型:2026年最新支持esim的手机型号与选购终极指南
Github无法访问:全面排错与解决方案,VPN、网络安全与速度优化指南