How to configure intune per app vpn for ios devices seamlessly
How to configure intune per app vpn for ios devices seamlessly is all about a streamlined setup that keeps apps secured without forcing a full device VPN. Quick fact: per-app VPN lets you tunnel only the apps you choose through a VPN, preserving battery life and improving performance for other apps. In this guide, you’ll get a practical, step-by-step walkthrough, plus real-world tips, best practices, and troubleshooting. Here’s a concise overview you can skim before digging in:
- What per-app VPN is and why it matters on iOS
- prerequisites you need before you start
- step-by-step configuration flow in Intune for iOS
- how to assign the profile to users and devices
- testing and validating the setup
- common issues and quick fixes
- security considerations and compliance
- roles and responsibilities in an IT team
- extra tips to scale across orgs
- quick reference checklist
Useful resources you might want to keep handy text only: Apple Website - apple.com, Microsoft Intune documentation - docs.microsoft.com, Intune per-app VPN overview - docs.microsoft.com, VPN vendor setup guides - vendor websites, IT admin blogs - various reputable sources
If you’re aiming to secure just the apps that handle sensitive data on iOS without turning every device into a VPN client, per-app VPN is the way to go. This guide gives you a practical, end-to-end plan to configure Intune per-app VPN for iOS devices seamlessly, with clear steps, screenshots-like descriptions, and troubleshooting tips. You’ll find a mix of step-by-step instructions, checklists, and quick-reference tables so you can implement it faster and with fewer headaches. Microsoft edge tiene vpn integrada como activarla y sus limites en 2026
What you’ll learn
- Why per-app VPN is valuable for iOS in enterprise environments
- The exact Intune setup flow for per-app VPN on iOS
- How to map apps to VPN profiles and assign them to user groups
- How to validate that traffic is correctly tunneled and apps stay responsive
- Common pitfalls and how to avoid them
- Security and compliance considerations when using per-app VPN
Prerequisites and basics Before you start, gather these essentials:
- An active Microsoft Intune tenant with appropriate admin rights
- A VPN gateway or service that supports per-app VPN on iOS for example, an Always-On VPN gateway or vendor-specific solution
- iOS devices enrolled in Intune MDM-enrolled devices
- An Apple Push Notification service APNs certificate deployed to Intune
- A KDC/Radius or cloud-based authentication if your VPN requires it
- The iOS device configuration profiles you’ll deploy via Intune
Now, let’s break down the configuration into actionable steps.
Step 1: Prepare your VPN service for per-app VPN
- Confirm that your VPN gateway supports per-app VPN for iOS and that you can export the required configuration IKEv2/IPsec, AnyConnect-like profiles, or vendor-specific formats.
- Obtain the following from your VPN provider:
- Server addresses
- Shared secret or certificate-based authentication details
- Supported protocols and port requirements
- Split-tunnel or full-tunnel configuration policy
- Create a dedicated VPN profile in your VPN service for iOS, with a test app mapping to the VPN connection if the vendor offers it.
Step 2: Ensure proper certs and APNs in Intune Nordvpn apk file the full guide to downloading and installing on android
- Upload or renew your APNs authentication key or certificate in the Apple MDM section of Intune.
- Verify that devices can check in with Apple and receive MDM commands.
- Ensure your VPN certificate if using certificate-based authentication is accessible to the Intune policy or included in the profile.
Step 3: Create a per-app VPN configuration in Intune
- Open the Intune admin center and go to Devices > Configuration profiles.
- Create a profile with:
- Platform: iOS/iPadOS
- Profile type: VPN
- Connection name: Give a clear, descriptive name e.g., “Per-App VPN – MyVPN for iOS Apps”
- VPN type: IKEv2 or L2TP/IPsec depending on your VPN gateway per vendor
- Server address, remote ID, and local ID as required by your VPN gateway
- Authentication method: certificate-based or username/password prefer certificate-based if supported
- Include a trusted root certificate if your VPN uses a private CA
- Set the app-based VPN mapping:
- In the App mapping section, add the apps that will use the VPN. You’ll typically specify bundle IDs for iOS apps e.g., com.apple.MobileSMS, com.yourcompany.yourapp.
- For each mapped app, ensure the VPN connection is forced when the app launches or when traffic to certain domains is detected, depending on the policy you want.
- Configure per-app VPN behavior:
- Enable “Connect on demand” or “Always-on” if your security posture requires it.
- Decide on the split-tunnel policy which traffic goes through VPN vs. direct based on your network design.
- Save and assign the profile to user or device groups see Step 5.
Step 4: Create a per-app VPN policy keying to apps
- Some vendors require an additional per-app VPN policy object to define app-to-VPN mappings.
- If your VPN solution integrates with Intune via a “per-app VPN” policy object, configure:
- App identifiers bundle IDs
- VPN connection name to associate
- Traffic rules and DNS settings if you’re routing only specific traffic
- Validate that the mapping is correctly aligned with the iOS apps you’ve chosen.
Step 5: Assign the profile to users or devices
- In the Intune console, assign the per-app VPN profile to the appropriate groups:
- Target groups by department, location, or device type
- Consider a pilot group first e.g., 5–10% of users to verify behavior
- Ensure there is a fallback flow if a device loses connection to the VPN gateway e.g., graceful degradation or user notification.
Step 6: Configure app deployment and ensure app compatibility
- Ensure the apps you mapped to the VPN are deployed to those devices.
- Some apps may have internal VPN negotiation requirements or require the VPN to be available before launch. Test these apps to confirm they launch and stay connected when required.
- For apps that don’t need VPN by default, ensure they don’t override the per-app VPN rule.
Step 7: Validation and testing Say Goodbye to Ads Your Ultimate Guide to Surfshark VPNs Ad Blocker and Beyond
- Enroll test iOS devices and apply the Intune per-app VPN policy.
- Verify:
- The mapped apps show VPN status as connected when opened.
- Non-mapped apps do not route through VPN if split-tunnel is used.
- Traffic for mapped apps reaches corporate resources securely.
- VPN disconnection scenarios work as expected e.g., when the device goes offline or VPN gateway becomes unreachable.
- Use iOS built-in diagnostics or your VPN provider’s diagnostics to test connections.
Step 8: Monitoring and reporting
- Use Intune reporting to monitor deployment status and device compliance.
- Monitor VPN gateway logs for authentication attempts, session durations, and error codes.
- Set up alerts for VPN connection failures or unusual traffic patterns.
Step 9: Security and compliance considerations
- Enforce device and app-level policies:
- Require passcodes, encryption, and device health checks.
- Enforce per-app VPN for sensitive apps to minimize data exposure.
- Consider data loss prevention DLP controls to restrict data movement from compliant apps.
- Regularly rotate VPN credentials and prune unused app mappings.
- Audit logs and retention: configure appropriate logging in both Intune and your VPN gateway.
Step 10: Troubleshooting quick playbook
- If an app can’t connect through VPN:
- Check the app’s bundle ID mapping and ensure it’s included.
- Verify the VPN profile is assigned to the device and is active.
- Confirm the VPN gateway is reachable and authentication succeeds.
- If VPN disconnects unexpectedly:
- Check for IP address changes on the device, network handoffs, or certificate expiration.
- Verify that the app is still mapped to the VPN after updates.
- If apps don’t launch or crash with VPN enabled:
- Review app compatibility with VPN timers and networking constraints.
- Check for any DNS resolution issues when the VPN is active.
- If notification prompts appear for VPN on iOS:
- Ensure privacy settings aren’t blocking VPN status notifications for the app.
Tables and quick-reference formats
- App mappings example
- App: com.yourcompany.salesapp
- VPN Profile: Per-App VPN – MyVPN
- Behavior: Always-on for this app, split-tunnel enabled
- VPN settings example
- VPN Type: IKEv2
- Server: vpn.yourcompany.com
- Remote ID: vpn.yourcompany.com
- Auth: Certificate-based
- Trusted CA: YourCompanyCA
Advanced optimization tips Лучшие vpn для геймеров пк в 2026 году полный обзор и выбор 2026 года
- Use grouping for app mappings: categorize apps by business function Sales, HR, Finance and apply consistent VPN rules to each group.
- Implement staged rollouts: begin with a small pilot, collect feedback, and gradually expand deployment.
- Integrate with conditional access: pair per-app VPN with conditional access policies to further restrict access to corporate resources based on user risk, device posture, or location.
- Consider battery and network usage: monitor VPN session lengths and optimize for idle time to preserve device battery life.
- Documentation and runbooks: maintain an internal runbook covering step-by-step deployment, common error codes, and escalation paths.
Real-world considerations
- User experience: explain to users what happens when they open mapped apps, including expectations about VPN status and data routing.
- App updates: when apps are updated, verify that the bundle IDs remain unchanged and mappings stay valid.
- Cross-organization scaling: when expanding to multiple geographies, ensure VPN gateways have regional redundancy and failover.
- Vendor-specific quirks: some VPN providers have unique settings for iOS, such as certificate pinning or extra DNS configurations; document any vendor-specific caveats.
Checklist
- VPN gateway supports per-app VPN on iOS
- iOS devices enrolled in Intune with APNs certificate configured
- VPN profile created in Intune with correct server and authentication method
- App mappings defined with accurate bundle IDs
- Per-app VPN policy assigned to the right groups
- Apps deployed to user/devices and tested
- Validation tests completed for connection, split-tunnel behavior, and failover
- Monitoring and alerts configured for VPN and device status
- Security policies aligned: encryption, passcodes, DLP, compliance checks
Frequently Asked Questions
What is per-app VPN in Intune for iOS?
Per-app VPN is a feature that tunnels traffic from selected iOS apps through a VPN gateway, while other apps on the device can bypass the VPN. This gives tighter control over which apps’ data is secured.
Why should I use per-app VPN instead of a device-wide VPN?
Per-app VPN saves battery, reduces needless network overhead for non-sensitive apps, and provides granular security by restricting VPN usage to only specified apps and data flows. Tuxler vpn edge extension your guide to secure and private browsing on microsoft edge
Which VPN protocols work best with iOS per-app VPN?
IKEv2/IPsec is common and well-supported for iOS. Some vendors support additional protocols or their own approaches; follow your VPN provider’s guidance for the best balance of security and performance.
How do I map an app to a VPN in Intune?
In a VPN configuration profile for iOS, you provide a list of app bundle IDs to attach to the VPN. When those apps start, traffic is routed through the VPN connection.
Can I use split tunneling with per-app VPN?
Yes, you can configure split tunneling so that only corporate resources go through the VPN while other traffic goes directly to the internet. This requires careful planning to avoid accidental data leakage.
What happens if the VPN connection drops?
If the VPN is required for the mapped apps, they may lose connectivity to corporate resources. Configure a graceful fallback or auto-reconnect behavior and ensure your apps can handle transient network changes.
How do I test a per-app VPN deployment?
Test with a small group of devices first. Open mapped apps and verify VPN is connected, then launch non-mapped apps to ensure they don’t route through the VPN. Check logs from Intune and your VPN gateway for successful connections and failures. Is radmin vpn safe for gaming your honest guide
Are there any common pitfalls with per-app VPN on iOS?
Common issues include incorrect app bundle IDs, misconfigured VPN server details, APNs issues, and certificate mismatches. Always validate with test devices and keep an updated runbook.
How long does it take to roll out per-app VPN to an organization?
A small pilot can be completed in a few days, depending on your environment. A full deployment across thousands of devices can take a few weeks, with phased rollout and ongoing monitoring.
Can users manually override per-app VPN?
By default, per-app VPN behavior is controlled by the configuration profile. You can design policies to prevent manual overrides, but you should communicate with users about how the VPN behaves to avoid confusion.
Appendix: quick example mappings illustrative
- Mapped App: com.yourcompany.salesapp
- VPN Profile: Per-App VPN – MyVPN
- Split Tunnel: Enabled only corporate resources through VPN
- Mapped App: com.yourcompany.hrapp
- VPN Profile: Per-App VPN – MyVPN
- Split Tunnel: Disabled full-tunnel for this app if required
Note: For best results, tailor the mappings to your organization’s apps and security posture, and keep your risk management team in the loop during rollout. If you need a deeper dive into specific vendor configurations or want a ready-to-use template, I can tailor a version for your VPN provider and Intune environment. And if you’re exploring security tools beyond VPN, consider pairing this with a strong endpoint protection and DLP strategy. Windscribe vpn extension for microsoft edge your ultimate guide in 2026
Sources:
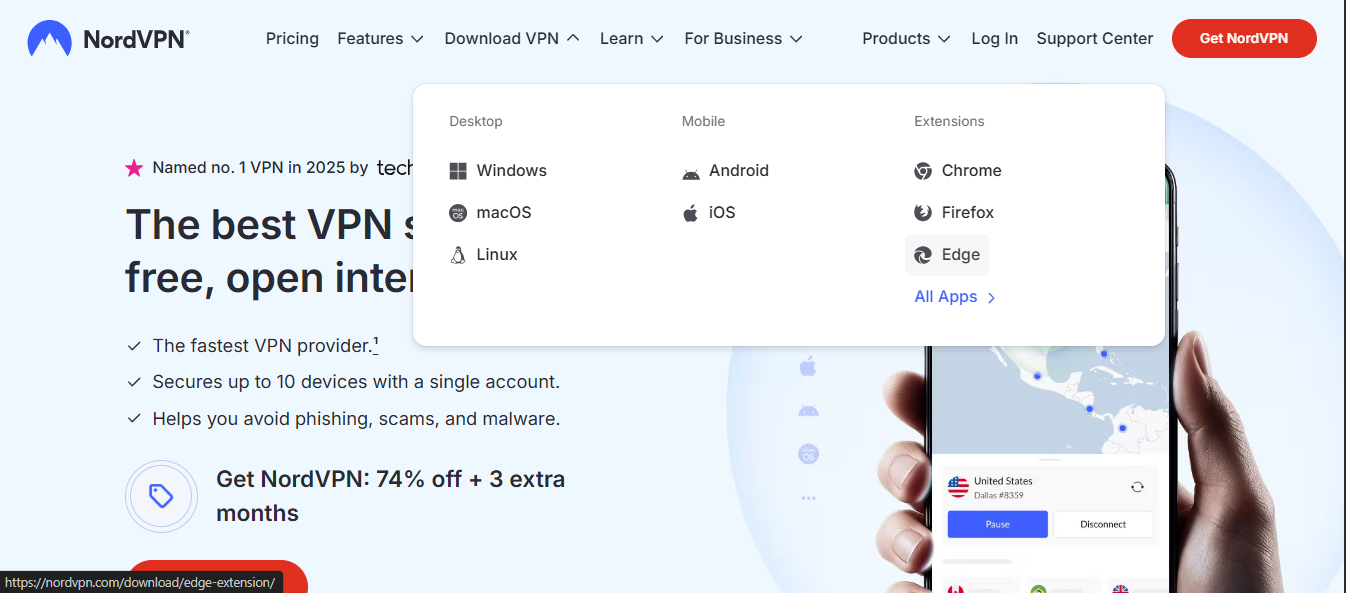
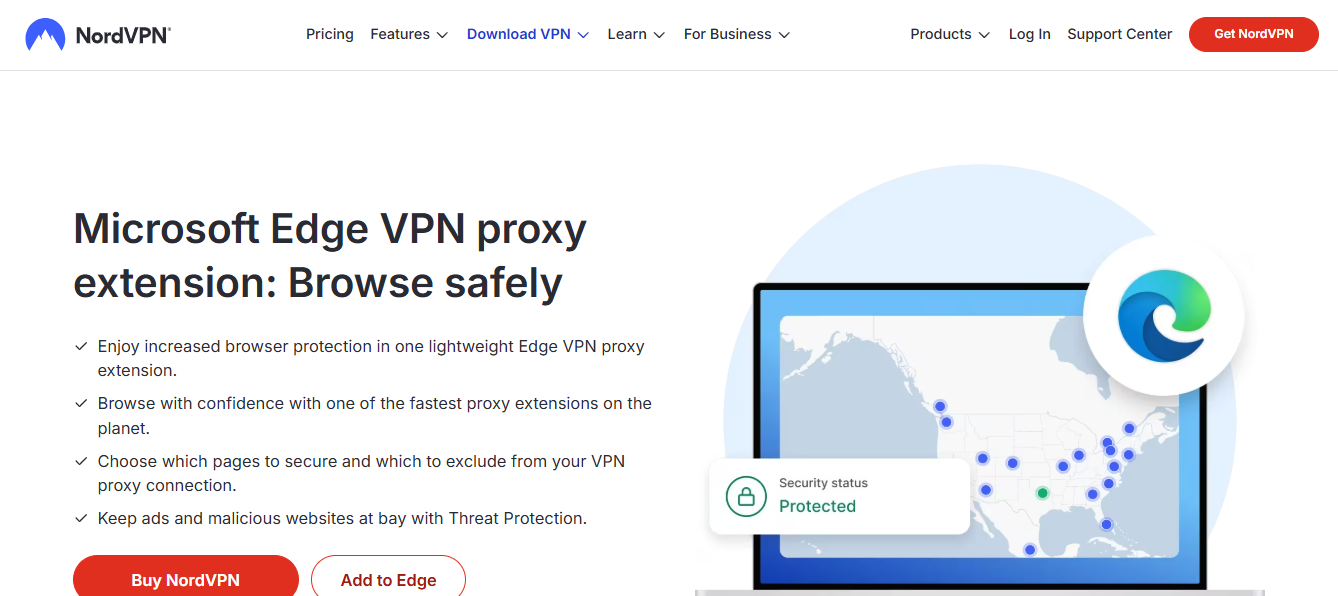
Nordvpn How Many Devices Can You Actually Use The Full Story: Everything You Need To Know For 2026
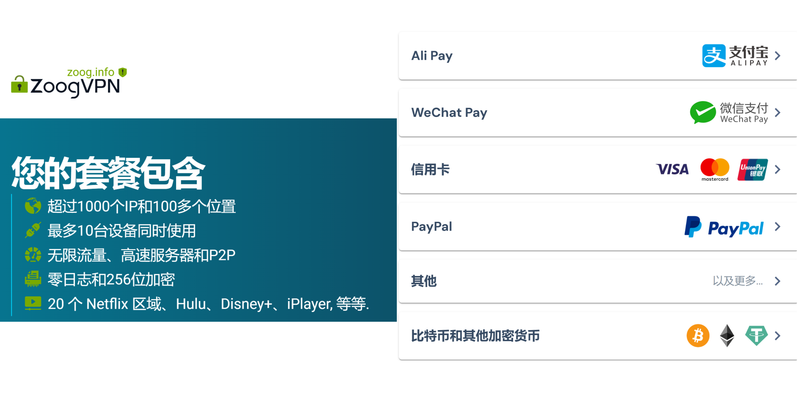
Edge secure network vpn free
Unifi nordvpn the ultimate combo for rock solid privacy security and beyond
Win10自帶vpn怎麼用|完整教學與實作技巧,快速上手 Win10自帶 VPN 設定與測試 Globalconnect vpn wont connect heres how to fix it fast: Quick fixes, tips, and pro tricks for a reliable connection